Phishing – attempts to trick people into giving up sensitive information – has been on the rise for many. many years now. Even seasoned internet individuals can fall prey to the bad actors perpetrating this criminal activity.
The Phish
Here is an example of a text I actually received on my Samsung android phone just this morning. I’ll try to outline my thoughts to – and the steps to ascertain whether it was a valid text – as best as possible here. I always wonder how many people’s lives are turned upside down because they fall for these. I saved the screenshot in landscape format so the phone number would show:
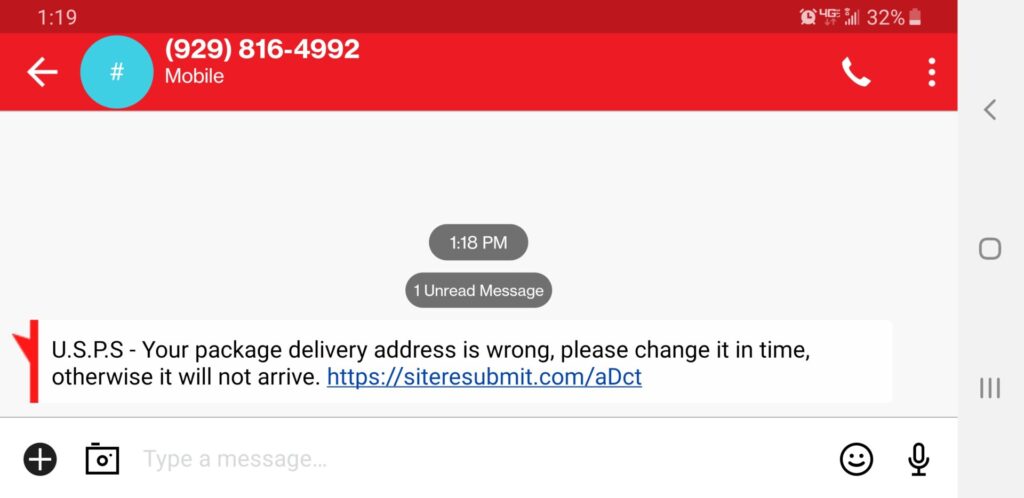
So there are a few things I noticed in particular about this message that are worth pointing out.
First of all, I was wondering why it came to my cell phone. I don’t usually use my cell number for such purposes, so that aroused my suspicions. However, I know that many people only have a cell phone, so that would not be out of the ordinary to receive a text about something being shipped to you. Unless, of course, you weren’t expecting anything to be shipped. Then you SHOULD be on high alert.
The next thing I thought about was that phone number. So, on my desktop, I looked up the phone number that this text came from by typing it into a Google search. Needless to say, looking up 929-816-4992 did not indicate it was attached to the U.S. Postal Service. Most legitimate phone numbers will yield something in a Google search indicating what they belong to. And the last thing to do is call a number on an unknown text. At best it is spoofed – meaning it is some unsuspecting person’s number who will have no idea why you are bothering them. At worst it is a number actually used by the scammer who will work as hard as possible to talk you out of your personal information. And, if you call, you are verifying that you got the message and it is a good number to attack in other ways or spam.
Finally there’s that domain name the sender wants me to go to. That really raised a red flag for me. I’ve been in computer, internet and web businesses one way or another for most of my life. I thought the domain name in the web address that this message wants to send me to was very suspicious. The text is indicating it is from “U.S.P.S.” which one might right off believe stands for the “United States Postal Service”. However, with the next steps I did, I’ll explain why I really believe the message is actually more likely from the “United States Phishing Service” (hopefully there’s really no such organization although nothing on the web surprises me anymore).
With that domain name AHA! moment, I next moved on to a step that may be new for most of you, but any of you with access to a web browser connected to the Internet can do this. The steps I followed are below. It took me way longer to write this out and will take you longer to read this than it takes to actually do it:
- First, simply navigate to:
https://research.domaintools.com/ - Once there, you will be presented with the ability to perform what is called a Whois Lookup on any existing domain name.
- In that search box, I typed the domain name of the web address the text was egging me on to visit:
siteresubmit.com - Then I clicked ENTER
- Then I clicked in the check box to indicate I was not a robot.
- Then I clicked on the “Go” button.
Behold, there is a wealth of information there about that domain name. At least to me, anyway. For me, it was enough to turn on all kinds of red lights, warnings, and many bells and whistles!
The first thing I always look for is how long the domain is in use. While there are some reasons that the creation date could be incorrect, that only happens rarely. For security purposes when investigating a suspicious text, it is not rocket science to notice that this domain was “Created on 2022-07-28”. So it has been online since just 3 days from my writing this article! I know the U.S. Post Office has been around just a little longer than that…
Now, armed with this information, you should report or otherwise block the text, as I did. In fact, find out how to report such phishing attempts on your phone or other device as phishing or at minimum as spam. You may have to ask your phone or email provider how to do this if you have to. The world will be a safer place if you do.
What You Can Do to Help Others
I hope this has been a little helpful in raising your awareness about several respects of phishing messages so you can:
- Be aware of the Universal Resource Locator (URL – a fancy phrase for the web address) that any email or text message or link on a website is sending you to.
- Be aware that you have the ability to look up a phone number in Google (or the search engine of your choice).
- Be aware that you have the ability to check on any domain name currently in use using the simple procedure I spelled out above.
- Be aware of how to report something on your phone or other device as phishing or at minimum as spam (ask your phone or email provider if you have to).
As long as there are people bad actors and scam artists can trick or con or fool into giving away their information, there will always be bad actors and scammers out there.
My hope is to reduce the number of those falling prey to those bad actors. Only then will it be less profitable to steal from people in this manner.
For more detailed information on phishing and suspicious behavior check out this directly from Microsoft:
https://support.microsoft.com/en-us/office/phishing-and-suspicious-behaviour-0d882ea5-eedc-4bed-aebc-079ffa1105a3
CharlesWorks is a Microsoft Partner. If you are not using Microsoft email yet, consider calling or texting us at +1 603-924-9867. Or contact us via our website at https://charlesworks.com/contact/. We are here to help get you hooked up.
I do not recommend performing the steps I did in this part of the process below – I’m just showing you here for informational purposes what I saw using special tools at my disposal.
Please Do Not Perform These Steps
I don’t recommend you perform the following steps. You could infect your machine or whatever device you are visiting the indicated site with. All I will show you here is what was displayed in several browsers and why I usually encourage people to use Google’s Chrome browser for their general Internet surfing.
I did these tests in what is called a virtual machine. That’s a disposable “fake machine” that I can do testing in and just delete it when I’m done. So there is no connection with the browser pages in it and my actual workstation. If you don’t have that at your disposal, you really should not subject your device to possible infection.
Here is what was displayed when I used Chrome:
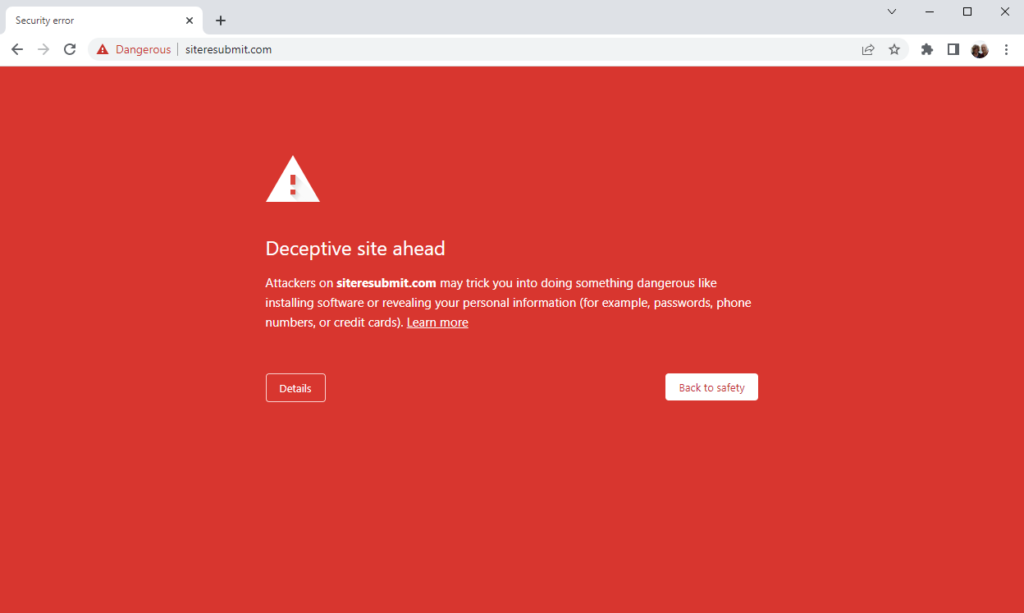
I would say this was excellent. What this means is that the fact that this was a phishing site was already reported to the powers that be at Google prior to my arrival there.
Here is what was displayed when I used Firefox:
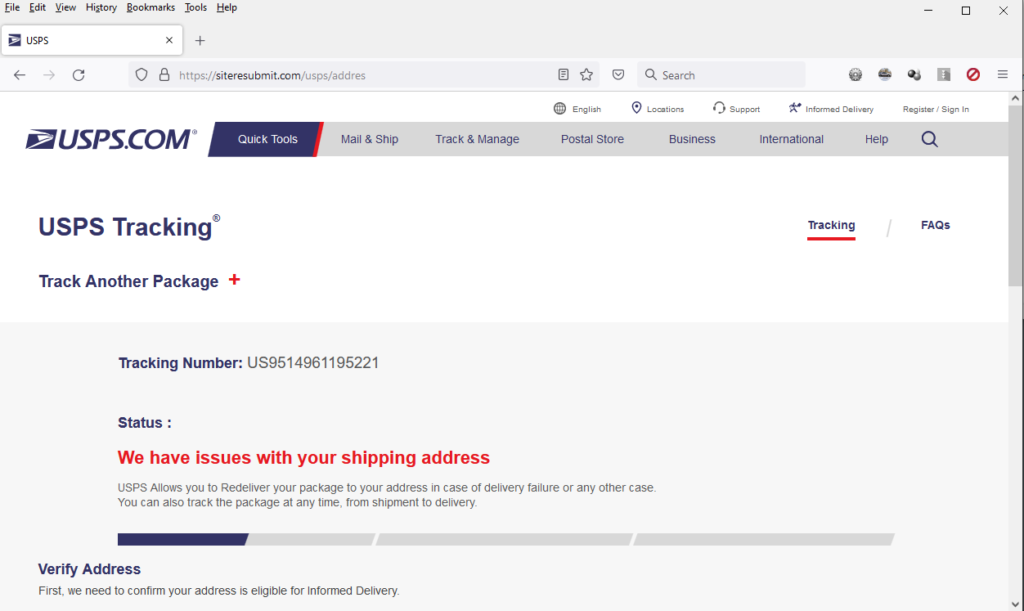
Firefox has not been made aware yet that this is a phishing site. Notice how it looks just like the U.S. Postal Service’s website! These bad actors are very good at what they do. However, the URL (web address) in the top of the browser page gives it away.
Here is what was displayed when I used Edge:
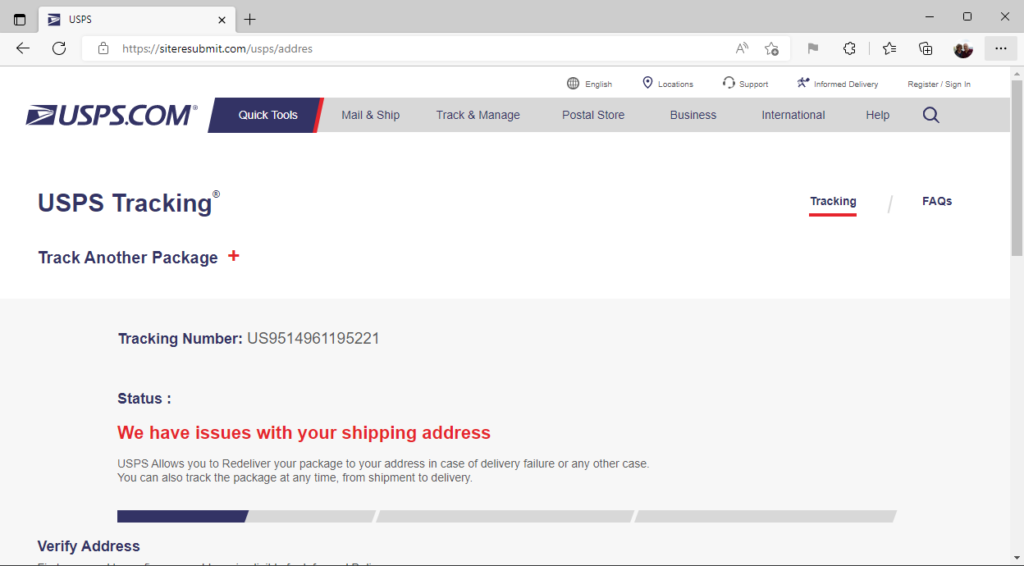
Edge also has not been made aware yet that this is a phishing site. Notice how it also looks just like the U.S. Postal Service’s website! As I said, these bad actors are very good at what they do. However, once again, the URL (web address) in the top of whatever browser page you are viewing the site in gives it away.
So to reiterate: Google has already received information that this was a phishing site. And Firefox and Edge were unaware at the time of my checking this today shortly after 1:19 pm eastern time.
Another tidbit I will share with you is that in this virtual machine I started with what is called a cleared internet cache. When I cleared my cache again after simply navigating to the address in each of the three browsers, here is what was cleaned:
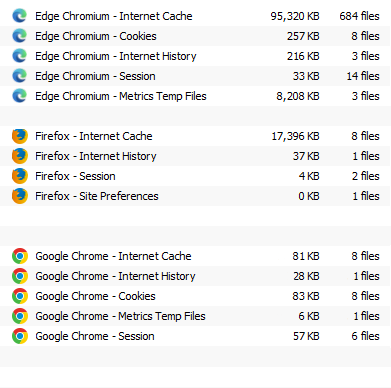
So, as you can see, there was actually a bunch of material downloaded when that page was loaded into each of the browsers. While it is way beyond the scope of this article to dig into what was downloaded by the browsers when visiting this phishing site, you can believe it isn’t good.
Contact CharlesWorks for Your Web Needs
We are always here to help. We provide website hosting which INCLUDES an SSL certificate to encrypt your site at no additional ongoing charge, website updating if and as you need it, automatic backups for the past month, and automatic WordPress core, theme and plugin updates to help prevent hacks due to software exploits.
Call or text us at 603-924-9867 or email us at Websites@CharlesWorks.com and we will do our best to help!


